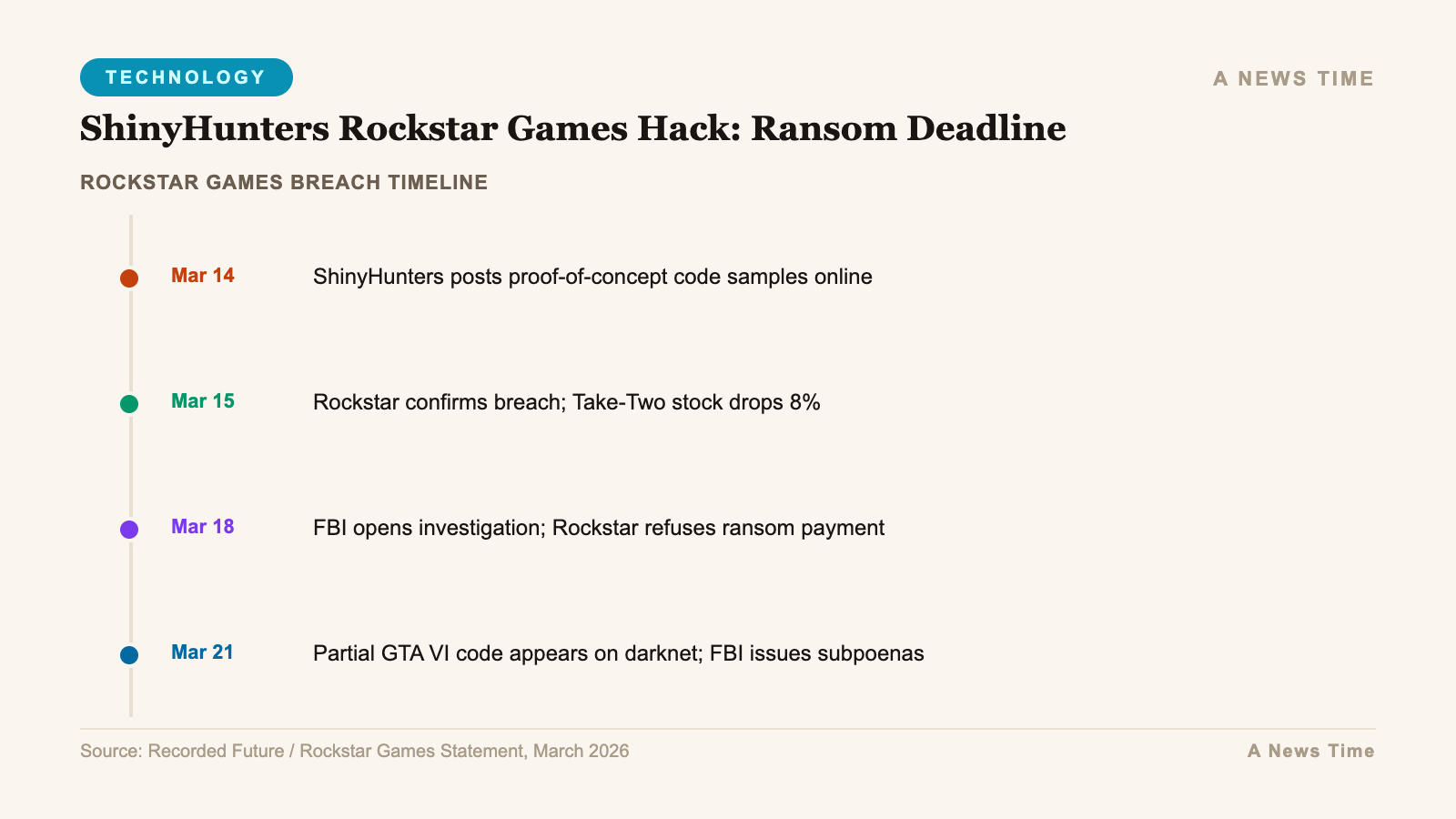
The cybercriminal group ShinyHunters, formally tracked by researchers as UNC6040, added Rockstar Games to its dark web leak site on or around , with a deadline of to pay or face public release of the stolen data. Rockstar confirmed the breach in a statement that described "a limited amount of non-material company information" having been accessed, adding that there was "no impact on our organization or our players." The confirmation, carefully worded to minimize disclosed scope, came after ShinyHunters had already made its threat public.
The attack vector identified by security researchers is a compromised SaaS cloud-cost monitoring tool called Anodot. The attackers used their access to Anodot to harvest authentication tokens with sufficient permissions to access Rockstar's Snowflake cloud data platform. Snowflake has been at the center of several high-profile breaches over the past year, as attackers have recognized that cloud data warehouses often hold consolidated copies of data from dozens of internal systems, making them high-value single points of compromise. For Rockstar, the Snowflake access potentially exposed whatever data the company had centralized there for analytics, cost management, and business intelligence purposes.

ShinyHunters: A Brief Profile of UNC6040
ShinyHunters is not an obscure threat actor. The group has been among the most prolific and damaging data extortion operations in recent years, with a track record that includes breaches affecting tens of millions of users across multiple major companies. Security vendor Mandiant's designation of the group as UNC6040 reflects the level of attention the group has received from professional threat intelligence teams.
Notable in the group's history is a claimed breach of a Google database, which they reportedly leveraged for its credential value. ShinyHunters typically operates on a dual-extortion model: steal data, demand payment, and publish to a dark web leak site if payment is not received. The group's leak site, which cycles through victims with countdowns and screenshots of stolen data samples, functions both as a payment pressure mechanism and as a reputation signal to the broader criminal marketplace. Being listed on the site with a specific deadline is intended to convey seriousness and create time pressure that may tip an organization toward payment.
The group's targeting of Rockstar through a supply chain vector rather than a direct intrusion reflects an evolution in sophisticated ransomware and extortion operations. Direct attacks on well-resourced technology companies with mature security teams are increasingly difficult. Attacks through third-party SaaS tools that have legitimate access to the target's infrastructure are more reliable because the security review applied to those third-party tools is typically less rigorous than the review applied to core internal systems.
The Anodot-to-Snowflake Attack Chain Explained
The attack chain in the Rockstar breach is worth tracing in detail because it illustrates a threat pattern that affects any organization using interconnected cloud services. Step one: attackers compromise an Anodot account used by Rockstar. The compromise method has not been publicly specified, but typical vectors include phishing, credential stuffing using passwords from prior breaches, or exploitation of an Anodot-side vulnerability. Step two: inside the Anodot environment, the attackers locate authentication tokens or API keys that Anodot uses to connect to Rockstar's other cloud platforms, including Snowflake. Step three: those tokens are used directly against Snowflake without needing to repeat any authentication against Rockstar's own identity infrastructure.
This attack chain has a specific security implication that the security practitioner "The Cybersecurity Guy" identified publicly after the breach: organizations need to rotate tokens that do not expire. Many SaaS integration tokens are configured with long or indefinite validity periods because the operational overhead of rotating them regularly is high. But non-expiring tokens represent a persistent vulnerability: once stolen, they remain valid indefinitely unless the organization actively revokes and replaces them. An attacker who steals a non-expiring Snowflake authentication token from an Anodot environment has standing access to whatever that token authorizes, potentially for months or years after the initial compromise, until someone notices or the organization rotates the credential.
The Snowflake platform is specifically worth understanding in this context. Snowflake is a cloud data warehouse that many large organizations use as a central repository for business analytics data. Because it integrates with dozens of internal and external data sources, it often holds a consolidated view of data that would otherwise be distributed across many separate systems. For a game publisher like Rockstar, Snowflake might contain player analytics, spending patterns, game telemetry, employee data used for business reporting, or financial metrics pulled from other systems. The breadth of what might be in a Snowflake environment makes it a high-value target for data thieves.
Rockstar's Second Major Breach: The 2022 Context
This is not the first time Rockstar Games has been the victim of a significant security breach. In September 2022, a hacker accessed the company's internal Slack workspace and posted approximately 90 clips of footage from the then-unreleased Grand Theft Auto VI, along with portions of the game's source code. The leak, described at the time as one of the most significant in video game history, exposed years of development work and confirmed details about the game's setting and characters that Rockstar had kept secret. The attacker behind the 2022 breach was later identified as a 17-year-old British national associated with the Lapsus$ group.
The 2022 breach and the current ShinyHunters incident share a supply chain adjacency: both involved attackers gaining access through platforms used for internal communication and collaboration rather than attacking Rockstar's game servers or core production systems directly. The 2022 attacker used compromised Slack credentials obtained through social engineering. The 2026 attacker used a compromised third-party monitoring tool to harvest cloud platform tokens. Different tools, same general pattern: find a lateral entry point through an adjacent platform where defenses are lower.
The pattern across both incidents suggests that Rockstar, like many large media and entertainment companies, has a more robust security posture around its core game infrastructure and intellectual property repositories than around the adjacent tooling ecosystem used for business operations. That asymmetry is common. Security teams tend to invest most heavily where they perceive the highest value to be. For a game company, the source code, the game builds, and the player-facing servers are the obvious high-value targets. The cloud cost monitoring tool, the internal Slack, and the business analytics warehouse receive less attention, even though they can provide pathways to the core systems or contain sensitive data in their own right.
What "Non-Material" Actually Means in Corporate Breach Language
Rockstar's public statement deserves some careful reading. The company said "a limited amount of non-material company information was accessed" and that there was "no impact on our organization or our players." This language is crafted to accomplish specific legal and reputational goals simultaneously. "Non-material" in a public company context is a term with specific meaning under securities law: it refers to information that would not be considered significant by a reasonable investor in evaluating the company's financial condition or prospects. Using it implies that even if the stolen data were disclosed publicly, it would not affect Take-Two Interactive's (Rockstar's parent company) stock price in a legally meaningful way.
"No impact on our organization or our players" is similarly calibrated. It does not say that no data was taken, or that the breach was trivial, or that no sensitive information was exposed. It says there was no operational impact, which is a narrower claim. Organizations use this language specifically because it is technically defensible, not because it comprehensively characterizes what happened.
The fact that ShinyHunters is listing Rockstar on a leak site with a specific payment deadline contradicts at least the spirit of "limited" and "non-material." Ransomware and extortion groups do not invest the operational resources to execute a breach, manage stolen data, and operate a dark web negotiation process for trivial quantities of non-sensitive information. The value of the threat depends on the value of the data. If the data were genuinely non-material, the extortion threat would be ineffective, and ShinyHunters would have no leverage.
The Snowflake Breach Pattern: Why This Keeps Happening
The Rockstar incident is part of a broader pattern of breaches enabled by compromised cloud platform credentials, with Snowflake environments appearing repeatedly as the data repository that attackers ultimately target. Several high-profile 2024 and 2025 breaches followed essentially the same pattern: attackers obtained credentials for a cloud identity provider or third-party tool, used those credentials to access Snowflake environments with weak or absent multi-factor authentication, and exfiltrated data from the cloud warehouse.
Snowflake has taken steps to improve its default security posture in response to the pattern of credential-based attacks, including introducing more aggressive MFA enforcement and session management controls. But the underlying problem is architectural. When organizations grant third-party tools authentication credentials with broad read access to their data infrastructure, they create attack surfaces that are difficult to monitor comprehensively. Each third-party integration is a potential entry point, and the total number of integrations at a large enterprise can be in the dozens or hundreds.
The recommended response is not to abandon cloud data platforms, which would be impractical, but to apply the principle of least privilege rigorously to integration credentials. A cost monitoring tool like Anodot needs access to billing metadata. It does not need access to player data, financial records, or other content stored in a Snowflake data warehouse. If the integration credentials Rockstar granted to Anodot were scoped correctly, the blast radius of the Anodot compromise would have been limited to billing and usage data. If they were over-privileged, as is common in many enterprise configurations, the attacker gained access to whatever Rockstar had in Snowflake without those scoping limits.
The April 14 Deadline: What Happens If Rockstar Does Not Pay
ShinyHunters' April 14 deadline functions as a negotiating mechanism. The standard playbook for extortion groups running dark web leak sites is as follows: list the victim, set a public deadline, engage in private negotiations where the demand is stated and potentially negotiated down, and either settle or publish. The publication of data on a dark web leak site does not end the harm; it creates a new phase in which the data circulates through criminal networks and eventually reaches buyers who may use it for secondary crimes.
Federal law enforcement guidance, including from the FBI, consistently recommends against paying ransoms and extortion demands. Payment does not guarantee that the data will not be published. Payment does not guarantee that copies of the data have not already been distributed to secondary parties. And payment directly funds the criminal infrastructure that enables the next attack, both against Rockstar and against other organizations. Rockstar has not publicly indicated whether it intends to negotiate or pay, and given its size and parent company resources, the expectation from observers is that it will not.
If Rockstar does not pay and ShinyHunters publishes the data, the character of what is published will determine the next phase of the story. If the data is primarily internal business analytics and cost management records, the incident will generate news coverage but limited downstream harm. If the data includes employee personal information, unreleased game assets, or player data, the implications are broader and more complex. Rockstar's statement that the breach involved "non-material" information is either accurate, in which case the publication will be anticlimactic, or it is an understatement, in which case the publication will prove it.
For related coverage, see our reporting on the Chrome zero-day CVE-2026-5281 exploited in the wild, Panera Bread's ransomware playbook and the 5.1 million user breach, and the CareCloud patient data breach.
What Organizations Using SaaS Tool Ecosystems Should Do Now
The Rockstar breach adds another data point to an increasingly clear picture of how sophisticated extortion groups are operating. The era of frontal assaults on a target organization's perimeter is giving way to methodical mapping of the target's third-party tool ecosystem, identification of the weakest link, and lateral movement from that entry point to high-value data repositories. The implication for organizations of any size is that security posture can no longer be evaluated solely based on the strength of core internal systems. It must account for every third-party integration that holds valid credentials to those systems.
The practical steps are concrete: audit all third-party SaaS tools currently holding authentication tokens for your cloud infrastructure; verify that each token is scoped to minimum necessary permissions; implement a regular rotation schedule for long-lived tokens, including those issued to monitoring and analytics tools that are often configured and forgotten; and ensure that your Snowflake or equivalent cloud warehouse environment has MFA enforcement and session token validation that would detect the use of harvested credentials from an unusual access pattern or location.
These are not novel recommendations. They appear in every major cybersecurity framework. The Rockstar breach is a reminder that the gap between knowing what to do and actually doing it remains wide, and that the cost of that gap is measured in ransomware deadlines and dark web listings.
Sources
- Forbes: ShinyHunters Sets April 14 Deadline for Rockstar Games After Breach via Anodot Tool (April 12, 2026)
- BleepingComputer: Rockstar Games confirms breach, ShinyHunters demands ransom by April 14 (April 2026)
- Wired: How ShinyHunters Got Into Rockstar Games Through a Cloud Cost Tool (April 2026)
- Dark Reading: SaaS Supply Chain Attacks Via Cloud Monitoring Tools: The Rockstar Pattern (April 2026)