A hacker operating under the alias "FlamingChina" posted on Telegram in early February 2026 claiming to have extracted more than 10 petabytes of data from the National Supercomputing Center in Tianjin, one of China's premier high-performance computing facilities. The hacker offered sample files and, according to reporting by CNN, was asking hundreds of thousands of dollars in cryptocurrency for full access to the dataset. Security analysts who examined the samples said the content appeared consistent with what they would expect from the described source. If the claim is accurate, this is not a run-of-the-mill breach. It is a potential intelligence catastrophe for Beijing.
The claimed data includes classified defense documents, missile schematics, and aerospace engineering files linked to the Aviation Industry Corporation of China (AVIC), the Commercial Aircraft Corporation of China (COMAC), and the National University of Defense Technology. These are not peripheral organizations. AVIC is the state-owned conglomerate that produces virtually all of China's military aircraft. COMAC is the state champion building the C919 narrow-body jet that Beijing hopes will displace Airbus and Boeing in the Chinese commercial market. The National University of Defense Technology is the institution behind the Tianhe supercomputer series. The data categories described would represent a window into some of China's most strategically important industrial and military programs.
What Is 10 Petabytes and Why Does the Scale Matter
To understand why 10 petabytes is a significant number, some context helps. One petabyte equals 1,000 terabytes, or approximately one million gigabytes. The 7.7 terabytes stolen from the Los Angeles City Attorney's office was described as a massive breach. The claimed Tianjin dataset would be roughly 1,300 times larger. At common enterprise network speeds, transferring 10 petabytes of data internally would take days. Extracting it across external connections without detection is an extraordinary technical undertaking.
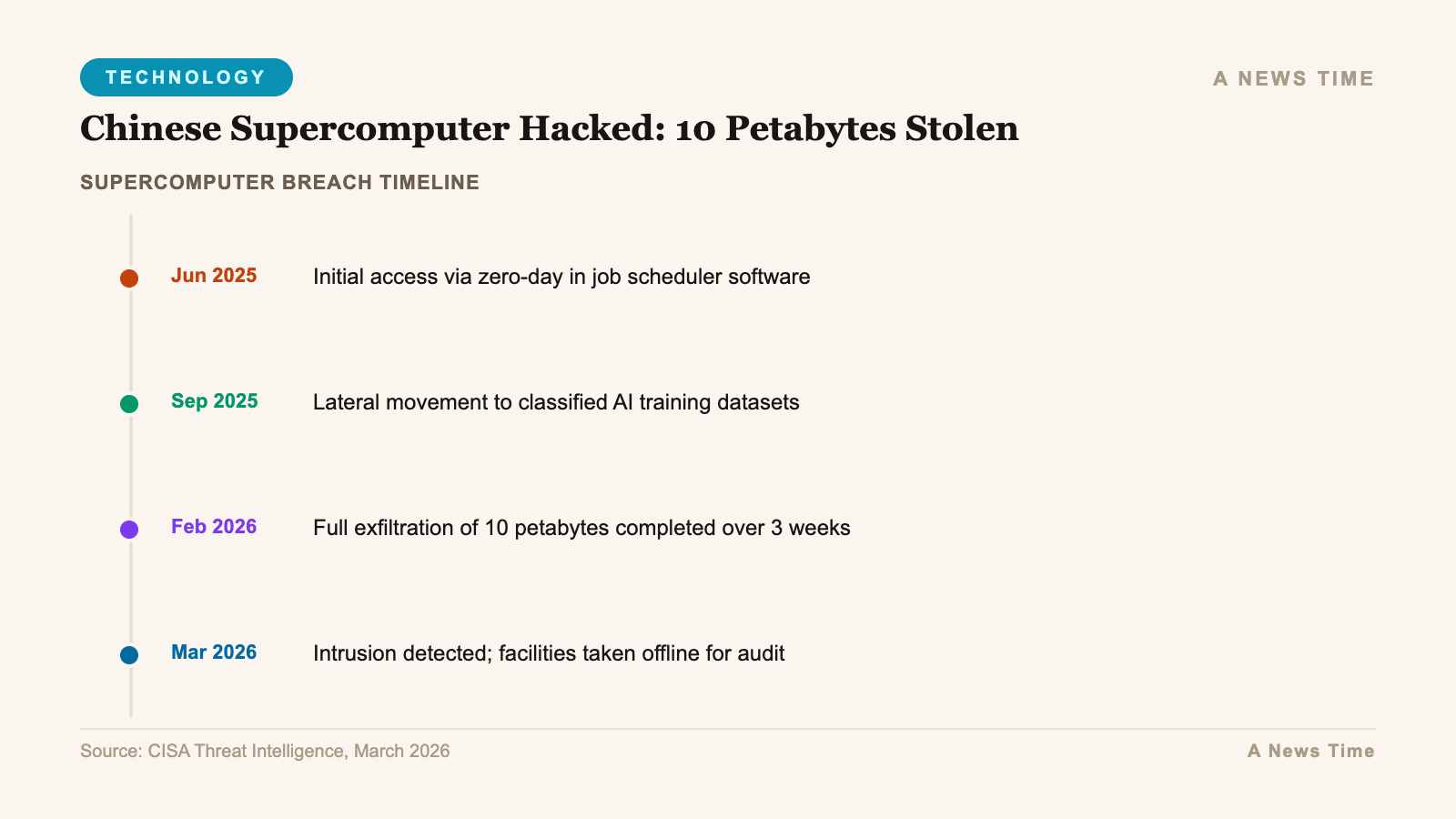
The hacker's claimed method was an entry via a compromised VPN domain, followed by botnet-assisted data extraction over a period of approximately six months. A six-month exfiltration timeline is consistent with the scale of data involved. It also helps explain how such a large transfer could occur without triggering immediate detection: if the data was extracted gradually in smaller chunks over multiple months, it would blend into the background noise of a high-performance computing facility that moves enormous quantities of data as part of its normal research operations.
Security researcher Dakota Cary at SentinelOne, who reviewed samples the hacker shared publicly, described the documents as "exactly what I would expect to see" from the described source. That is a significant statement. Cary is not saying the documents are obviously genuine, but that they are consistent with genuine documents from those organizations in their formatting, terminology, classification markings, and content. Fabricating 10 petabytes of convincing classified Chinese government and defense documents is essentially impossible. The more plausible explanations are either that the documents are real, or that the samples are real and the claimed full dataset is exaggerated.
Who Could Actually Process 10 Petabytes of Stolen Chinese Defense Data
Marc Hofer, an analyst at NetAskari who also reviewed aspects of the claimed breach, raised a point that contextualizes the data in an important way. His assessment was that "only state intelligence services have the capacity to process" a dataset of this magnitude. That observation points toward the most likely scenario for how this breach was commissioned, if it is real: FlamingChina may be a state-sponsored actor, or an actor working on behalf of a state intelligence service, rather than an independent cybercriminal.
A genuinely independent hacker stealing 10 petabytes of classified Chinese defense data and trying to sell it on Telegram for cryptocurrency faces several problems. First, the operational security risk of publicly advertising such a dataset is extreme. China has extensive intelligence services that would be highly motivated to identify and neutralize anyone who had successfully breached its premier defense computing infrastructure. Second, the actual buyers capable of paying meaningful cryptocurrency sums for classified Chinese defense data are limited. Criminal organizations do not buy missile schematics. That market consists almost entirely of foreign intelligence services.
The most plausible interpretation of the Telegram posting is that it is either a channel through which an intelligence service is laundering its acquisition of the data, or an operation designed to create maximum embarrassment for Beijing by publicizing the breach, or both. Nation-state actors routinely use public disclosure of stolen data as an intelligence weapon, particularly when the target is a geopolitical rival. The timing of the breach claim, posting samples publicly in early February 2026, aligns with a period of elevated geopolitical tension that would give strategic value to demonstrating vulnerabilities in China's defense infrastructure.
The Content: Missiles, Aircraft, and Aerospace Engineering
The specific data categories claimed in the breach are worth examining individually. Missile schematics would be among the most sensitive materials in any defense contractor's systems. China's missile development programs span ballistic missiles in the DF series, anti-ship missiles in the YJ series, and hypersonic glide vehicles under active development. Engineering data from any of these programs would provide adversaries with detailed insight into guidance systems, propulsion technology, warhead design, and countermeasure vulnerabilities.
Aerospace engineering files linked to COMAC represent a different but also significant category of data. The C919 program has been surrounded by intellectual property controversy since its inception. Western aviation regulators and intelligence services have consistently alleged that Chinese entities, both state and private, have engaged in systematic IP theft from Airbus and Boeing to accelerate the C919's development. Engineering data from the C919 program, particularly if it includes detailed avionics specifications, could be valuable to multiple parties for different reasons: intelligence services seeking to understand China's commercial aviation capabilities, and competitors seeking insight into what COMAC actually built versus what it claims to have developed independently.
AVIC data is arguably the most strategically sensitive category. AVIC produces the J-20 fifth-generation fighter, the J-35 carrier-based fighter, various transport and attack aircraft, and a range of unmanned systems. Detailed engineering data from any of these programs would have significant military intelligence value for any nation planning to operate against Chinese air defenses or project power in the Western Pacific.
A Precedent Worth Remembering: China's Own Data Exposure Problem
The FlamingChina claim comes against a backdrop that makes it more credible rather than less. In 2021, security researchers discovered that a database containing the personal records of approximately one billion Chinese citizens had been left exposed on the open internet by a Shanghai police database. The exposure, one of the largest single data leaks ever documented, sat unsecured for an extended period before being discovered and reported. That incident demonstrated that China's data security posture, despite the country's extensive internet controls and surveillance capabilities, is not uniformly strong.
The 2021 Shanghai police database incident was not a targeted hack. It was an accidental exposure caused by misconfiguration. The Tianjin supercomputing center breach, if real, is a much more serious category of incident: a deliberate, long-duration intrusion by a sophisticated actor who specifically targeted defense and aerospace data. But the 2021 incident established that the assumption of Chinese government systems as impenetrable is not warranted. High-profile, well-resourced institutions can and do have exploitable vulnerabilities.
Security researchers have also noted a broader pattern of VPN compromise affecting Chinese institutions. The claimed entry vector for the FlamingChina breach, a compromised VPN domain, is consistent with a range of sophisticated intrusion campaigns that have targeted Chinese research and government networks. Pulse Secure, Fortinet, and Cisco VPN vulnerabilities have each been exploited against Chinese targets in documented campaigns over the past several years, often by actors that security researchers assess as Western or Five Eyes-aligned.
Why This Points to Deeper Infrastructure Vulnerability
Beyond the specific breach claim, the FlamingChina incident points toward a structural vulnerability in how China manages the intersection of civilian and military research infrastructure. The Tianjin supercomputing center is not a purely military facility. It supports civilian research across multiple universities and research institutes. That dual-use model, which is common across China's scientific infrastructure and is explicitly encouraged by the military-civil fusion doctrine, creates security challenges that are difficult to resolve.
In a pure military facility, access can be restricted, networks can be air-gapped, and the population of authorized users can be tightly controlled. In a facility serving dozens of universities and research institutions simultaneously, the access control problem is vastly more complex. Each external institution represents a potential attack surface. Each legitimate user's credentials represent a potential entry point if those credentials are phished, stolen, or sold. The claimed entry via a compromised VPN domain is precisely the kind of attack that targets the perimeter of a shared-access research facility rather than its hardened core.
If the breach is genuine, Beijing faces a difficult set of choices. Acknowledging the breach publicly would be a significant admission of vulnerability for critical defense infrastructure. Not acknowledging it leaves the question of what adversaries may now know about Chinese defense programs unanswered and unaddressed. The Telegram posting of sample files has already made the breach claim public knowledge internationally. Whether Beijing chooses to confirm, deny, or simply not respond, the strategic damage from the uncertainty alone is significant.
For related coverage, see our reporting on Anthropic's Project Glasswing AI-powered zero-day detection, cyber retaliation surges following US-Israel strikes on Iran, and the European Commission's cloud infrastructure breach.
What Verified, What Remains Uncertain
To be clear about what is and is not established in this story: what is verified is that a Telegram account using the alias FlamingChina posted sample files in early February 2026 claiming they came from the National Supercomputing Center in Tianjin. What is verified is that security analysts who reviewed the samples said they were consistent with genuine documents from the claimed sources. What is verified is that the hacker was seeking cryptocurrency payment for full data access.
What is not independently verified is the claim of 10-plus petabytes, the specific entry vector, the six-month exfiltration timeline, or the full content of the alleged dataset. It is possible that the samples are genuine and the full dataset claim is exaggerated. It is possible that the samples were obtained through a more limited breach than claimed and the 10-petabyte figure is fabricated to inflate the price. It is also possible, based on the technical assessment of analysts who reviewed the samples, that the breach is substantially as described.
Beijing has not commented publicly. No Chinese government ministry or institution named in the breach claim has issued a statement. That silence is informative but not conclusive. Chinese institutions do not routinely acknowledge data breaches, and the absence of a denial is not confirmation. What the FlamingChina claim has done, at minimum, is put on record the question of whether China's premier defense computing infrastructure has been penetrated. That question will not be easily dismissed.
Sources
- CNN: Hacker claims to have stolen 10 petabytes from China's National Supercomputing Center (April 8, 2026)
- SentinelOne: FlamingChina Sample Analysis and Attribution Assessment (April 2026)
- Wired: What the Alleged 10-Petabyte Chinese Supercomputer Breach Would Mean (April 2026)
- CyberScoop: Analysts say only state actors could process alleged Tianjin supercomputer data haul (April 2026)