A ransomware group has leaked a massive trove of Los Angeles Police Department records after breaching the office of LA City Attorney Hydee Feldstein Soto. The stolen data, totaling 7.7 terabytes and comprising approximately 337,000 files, includes some of the most sensitive material that exists in local law enforcement: Internal Affairs investigations, officer personnel records, personal health information, and witness interview transcripts. City Attorney Feldstein Soto first became aware of the intrusion on , the same day the ransomware group claimed it had secured access to the system.
The scale and sensitivity of the stolen files have set off alarms across multiple stakeholders. The LAPD Police Protective League, the union representing rank-and-file officers, issued a sharp public rebuke of the City Attorney's office for failing to notify them promptly. The FBI confirmed it is "aware of the incident, is actively assisting." And legal observers are watching closely, because the breach of law enforcement personnel files is not just a privacy incident. For some officers, the exposure of their identities could be a physical safety issue. For others already named in litigation from a prior 2023 LAPD data release, this second exposure may compound existing legal exposure in complex and difficult-to-predict ways.
What Was Stolen: 7.7 Terabytes of the LAPD's Most Sensitive Files
Seven-point-seven terabytes is a substantial volume of data. To put it in context, a standard office workstation might hold two to four terabytes. A full terabyte of text documents could contain millions of individual files. The 337,000 file count suggests a mix of document types, likely including PDFs, Word documents, spreadsheets, images, audio files from witness interviews, and potentially video evidence that had been submitted to or processed by the City Attorney's office in the course of its prosecutorial and civil functions.
The file categories publicly identified as part of the stolen data include Internal Affairs investigations, which are the disciplinary records of officers under review for alleged misconduct; officer personnel files, which contain employment history, assignments, and personal identifying information; personal health information, which triggers specific legal obligations under HIPAA and California's Confidentiality of Medical Information Act; and witness interview records, which are particularly sensitive because witnesses in criminal and civil cases involving law enforcement often cooperate with the expectation that their identities will be protected.
Internal Affairs records are among the most legally controlled documents in law enforcement. California has extensive statutory protections for officer personnel files, codified in the Public Safety Officers Procedural Bill of Rights Act and Penal Code Section 832.7. These protections exist partly to prevent harassment of officers, but in the context of a data breach they create a secondary problem: the files exist precisely because they document alleged misconduct, and their unauthorized disclosure creates complex questions about both the privacy rights of accused officers and the interests of complainants whose names appear in those same documents.
The Attack Vector: A Third-Party File Transfer Tool
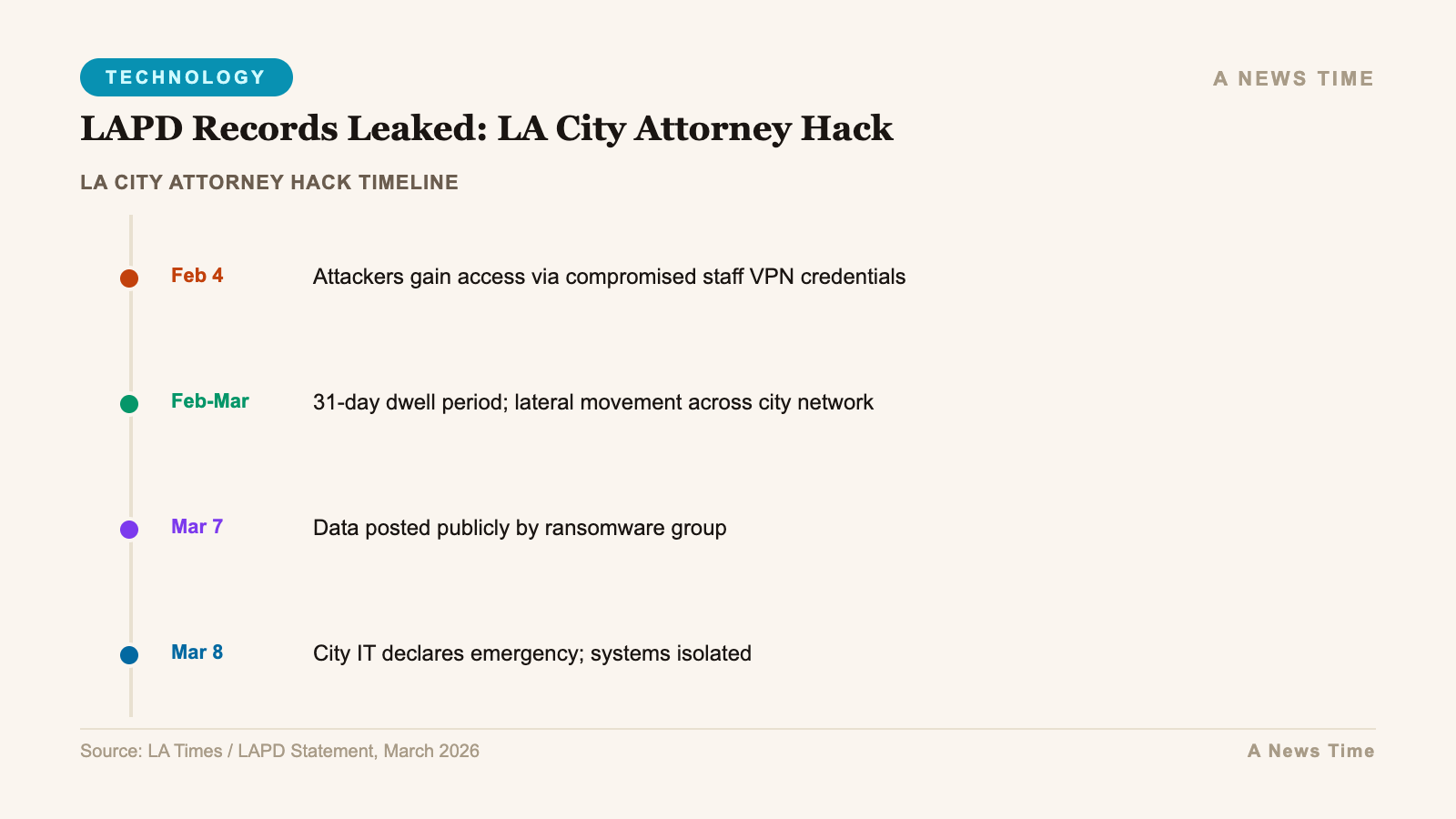
According to reporting on the incident, the attackers gained entry through a compromised third-party file transfer tool that the City Attorney's office used to transmit or receive documents. This attack vector has become one of the most reliable entry points for ransomware groups and data thieves over the past several years, for a straightforward structural reason: organizations routinely share sensitive documents with external parties, and the tools used to do this often receive less security scrutiny than internal systems.
The precedent here is well established. The MOVEit zero-day exploitation in 2023 compromised hundreds of organizations globally, from government agencies to pension funds, all because a file transfer utility sat at the perimeter of their networks with insufficient protections. Cleo and GoAnywhere vulnerabilities produced similar cascades. When a file transfer tool is compromised, it typically gives attackers access not just to files in transit but to everything that has been transmitted through the system, potentially including historical archives depending on the tool's configuration and retention settings.
The City Attorney's office has not publicly identified which specific tool was compromised. That detail matters for understanding whether other organizations using the same tool may also be at risk, and whether the vendor issued any advisories or patches around the time of the attack. The FBI's involvement suggests the investigation is examining the full attack chain, including whether the compromise was targeted specifically at the City Attorney's office or was part of a broader opportunistic campaign affecting multiple users of the same platform.
Police Protective League: "They Should Have Told Us Immediately"
The LAPD Police Protective League's public criticism of the City Attorney's office centers on the failure to notify officers promptly after the breach was discovered. The union's concern is not abstract. Police officers, particularly those with undercover assignments, those who have testified against organized crime figures, those involved in gang enforcement, or those who have received credible threats, have a genuine physical safety interest in knowing that their personnel records have been leaked. Personnel files typically contain home addresses, emergency contact information, vehicle registration data, and other personally identifying details that could be exploited by individuals with hostile intent toward law enforcement.
The union has pointed out that officers cannot take protective steps, such as changing their addresses with the DMV, alerting family members, or seeking protective orders, until they know they are at risk. Every day between the City Attorney's discovery of the breach on March 20 and formal notification to affected officers is a day when officers who may be at elevated risk have no information to act on.
The tension between the City Attorney's obligation to conduct a thorough investigation before notifying and the officers' interest in timely notification is a version of a conflict that plays out in virtually every large institutional breach. Organizations consistently argue that they need time to scope the breach accurately before sending notifications, partly for legal reasons (notifications that turn out to be inaccurate create their own liability) and partly for practical reasons (individual notifications require knowing whose data was affected). In cases where the at-risk population includes people with physical safety concerns, that calculus is harder to defend.
The 900-Officer Lawsuit Backdrop
This breach does not occur in a vacuum. Approximately 900 LAPD officers are currently suing the city over a prior 2023 data release. The 2023 incident, which reportedly involved the inadvertent disclosure of officer identifying information, established both a legal precedent for officer-plaintiff standing in breach-related litigation and a pool of attorneys who are already versed in the relevant facts and legal theories. For those 900 officers, this second breach is not a standalone event. It is an additional data point in ongoing litigation about the city's data handling practices, and potentially a basis for amending existing complaints or adding new claims.
For the broader population of officers whose information was not part of the 2023 litigation but who are now potentially affected by the 2026 breach, the 900-officer lawsuit provides a roadmap. California's breach notification laws, combined with the state's robust privacy litigation history, mean that class certification in cases involving large numbers of similarly situated plaintiffs is a well-tested framework. A 337,000-file breach spanning multiple categories of sensitive personal and professional information, from a government entity with a prior breach record, is precisely the kind of incident that plaintiff-side privacy litigation firms build cases around.
The city's exposure is compounded by the nature of the stolen data. Personal health information in the files triggers not just California breach notification requirements but potentially federal HIPAA obligations depending on how that information was collected and used. Witness interview records create additional concerns about the safety of civilian witnesses and potential interference with ongoing prosecutions if the leaked files relate to pending cases.
LA Metro Also Recently Hacked: A Pattern Emerges
The City Attorney breach comes against the backdrop of a separate, recent hack affecting LA Metro, the regional transit authority. While the two incidents appear to be independent, their proximity in time has drawn attention to what critics describe as a systemic problem with cybersecurity posture across major Los Angeles public institutions. The city has faced sustained pressure to modernize its IT infrastructure, and incidents like these provide concrete evidence of the consequences when that modernization lags.
Large municipal governments face a structural cybersecurity challenge that is distinct from the challenge facing private sector organizations. They operate with constrained budgets, often maintain legacy systems because replacement requires capital appropriations that move slowly through political processes, handle an enormous diversity of data types across many departments, and rely heavily on third-party vendors and interagency data sharing arrangements that each represent a potential attack surface. The file transfer tool compromise at the City Attorney's office illustrates this last point: even if the office's internal systems were reasonably hardened, the connection to an external tool became the entry point.
Security researchers who track ransomware groups have noted an increase in attacks targeting local and county government offices rather than the more prominent federal targets. The reasoning is largely opportunistic. Local governments often have weaker defenses, are more likely to pay ransoms because they cannot afford operational disruption, and hold data that is valuable both for direct exploitation and for intelligence purposes. A city attorney's office in a major metropolitan area is a particularly attractive target because of the breadth of data that flows through it: criminal records, civil litigation files, law enforcement documents, personnel records, and potentially records relating to confidential informants or undercover operations.
What the LAPD and City Hall Must Do Now
The immediate priorities for the City Attorney's office and the LAPD are notification and containment. Notification means identifying which officers' files were in the stolen dataset, determining what specific information about each officer was included, and delivering individual notices that give officers enough information to take protective action. For officers with safety-sensitive assignments, notification should be happening in real time, not waiting for a comprehensive forensic report.
Containment means verifying that the attacker no longer has active access to any city systems, that the compromised file transfer tool has been taken offline or patched, and that any other systems that communicated with the compromised tool have been examined for indicators of compromise. It also means auditing which other city agencies used the same tool, because a file transfer utility used by the City Attorney's office almost certainly also processed files for other city departments, each of which may hold its own category of sensitive data.
Longer term, the breach should prompt a formal review of third-party vendor security requirements across city agencies. The city's contracts with software vendors, particularly those handling sensitive law enforcement or personnel data, should include security baseline requirements, audit rights, and breach notification obligations running from the vendor to the city. If those contract provisions exist, this incident will test whether they are being enforced. If they do not exist, this incident makes the case for why they should.
For affected officers, the practical steps are familiar to anyone who has navigated a major identity breach. Credit monitoring enrollment, address confidentiality program participation where available, and direct communication with the City Attorney's office to understand exactly what information about them was in the stolen files. That last step is the hardest: organizations rarely provide individualized disclosure about what specifically was taken for any given person, citing the complexity of forensic analysis. But for officers whose safety depends on address confidentiality, general breach notifications are not adequate. They need to know specifically what was in their files.
The Ransomware Group and What Comes Next
Ransomware groups that publicly claim access to stolen data typically do so as leverage: pay, or the data gets published on a leak site. The dynamics of this incident are somewhat different from a standard ransomware case because the data involved is law enforcement records rather than financial or health data that the victim organization would most want to keep private. The City Attorney's office has strong legal and ethical reasons not to pay ransoms, and federal law enforcement guidance consistently recommends against ransom payment. The FBI's active involvement further constrains the city's options.
If the group follows the standard leak site playbook, the 337,000 files may end up publicly available on dark web forums or Telegram channels. That prospect is what makes rapid notification to affected officers so critical. Once the data is public, the window for protective action narrows considerably. The question is not whether the leak will happen but how much time exists between now and when it does.
The broader implications of this breach extend beyond Los Angeles. Law enforcement personnel files, Internal Affairs records, and witness interview transcripts held by city attorneys, public defenders, and court systems represent a category of data that has historically been assumed to be secure because of its sensitivity. That assumption is no longer warranted. As ransomware groups and state-sponsored actors grow more sophisticated and more focused on high-value institutional targets, organizations that hold sensitive law enforcement data need to treat that data as the high-risk asset it is, with security controls to match.
For internal links to related coverage, see our reporting on the Chrome zero-day actively exploited in April 2026, the European Commission's cloud breach on AWS, and Panera Bread's 5.1 million user ransomware incident.
Sources
- Los Angeles Times: Ransomware group hacked LA city attorney, leaked 7.7TB of LAPD records (April 7, 2026)
- NBC Los Angeles: FBI assists in investigation of LA City Attorney data breach (April 7, 2026)
- ABC7 Los Angeles: Police Protective League criticizes City Attorney over LAPD records leak (April 7, 2026)
- California Attorney General: Data Breach Notifications Registry













