On , three separate cybersecurity developments landed within hours of each other, painting a picture of a threat environment that is both more automated and more broadly targeted than at any prior point in the decade. A fast-growing RaaS operation called Gentlemen expanded its victim count past 320 enterprises. The U.S. CISA added a Cisco SD-WAN Manager information-disclosure flaw to its Known Exploited Vulnerabilities catalog and ordered federal agencies to patch by Friday. And Citizens Bank confirmed a vendor data incident even as ransomware actors claimed to possess millions of customer records. Meanwhile, Cognyte's LUMINAR 2026 Annual Threat Report, released the same day, placed the full-year 2025 context around all three events: nearly 50,000 new vulnerabilities disclosed, AI now automating up to 90 percent of specific nation-state espionage campaigns, and stolen credentials still showing up in 22 percent of data breaches.
Taken together, these incidents are not anomalies. They are the daily operating conditions of enterprise security in 2026.
Gentlemen RaaS: A Multi-Platform Threat Built for Enterprise Networks
The most technically detailed story of the 48-hour period came from Check Point Research, which published a full incident-response breakdown of the Gentlemen ransomware operation on April 21. The group emerged around mid-2025 and rapidly built an affiliate program by advertising on underground forums, positioning itself as tooling for "skilled penetration testers" rather than script kiddies. That framing is largely accurate: Gentlemen's affiliates follow a disciplined, multi-stage intrusion playbook that security teams would recognize from more established RaaS families.
Gentlemen's core locker is written in Go and runs on Windows, Linux, NAS, and BSD systems from a single command-line binary. The mandatory --password flag, which must match a value hard-coded inside the binary before encryption begins, is an anti-analysis feature designed to prevent automated sandbox detonation. The group additionally ships a separate locker compiled as an ELF binary in C, optimized specifically for VMware ESXi hypervisors. Before encrypting virtual disk files, this ESXi variant enumerates all running VMs, attempts a graceful shutdown of each, then force-kills any remaining processes to ensure VMFS files are fully unlocked and accessible for encryption. It then persists by copying itself as bin/vmware-authd and adding cron entries and boot-time scripts to survive reboots.
"Gentlemen's success rests on a mature, repeatable playbook: domain-level compromise, tool-driven lateral movement, endpoint detection and response suppression, and multi-platform lockers that reach both physical and virtual infrastructure."
Check Point Research, DFIR Incident Report, April 2026
In a documented enterprise intrusion, a Gentlemen affiliate obtained domain admin credentials, then used Cobalt Strike beacons pushed via administrative shares to fan across the network. The attacker ran standard discovery commands, accessed internal documentation to map the environment, and attempted to install SystemBC as a covert SOCKS5 tunnel. The affiliate also installed AnyDesk with a hard-coded password and used Mimikatz to harvest additional credentials from memory before detonating the locker across domain-joined systems via PowerShell and Group Policy. Telemetry from Check Point links Gentlemen affiliates to a SystemBC botnet of more than 1,570 compromised hosts, the vast majority corporate rather than residential.
The encryption modes, labeled "fast," "superfast," and "ultrafast," encrypt only 9 percent, 3 percent, or 1 percent of large file contents respectively, rendering files unusable while dramatically accelerating the encryption process. The underlying cryptographic scheme uses X25519 key exchange and XChaCha20 stream encryption, both well-regarded modern primitives that make brute-force decryption infeasible without the attacker's key. Gentlemen's Tor-hosted leak site, where it publishes stolen data when victims refuse to pay, implements the classic double-extortion model that became industry-standard practice among ransomware groups after 2020.
CISA's Cisco SD-WAN Emergency Order: Four Days to Patch
Parallel to the Gentlemen disclosure, CISA on added CVE-2026-20133 to its Known Exploited Vulnerabilities catalog, ordering all Federal Civilian Executive Branch agencies to secure their Cisco Catalyst SD-WAN Manager deployments by . The vulnerability, which Cisco patched in late February, allows unauthenticated remote attackers to read sensitive information from the underlying operating system by accessing the device's API without valid credentials.
According to BleepingComputer reporting on the CISA order, Cisco's own Product Security Incident Response Team had not confirmed active exploitation as of the Monday notice, with Cisco's advisory still stating it was "not aware of any public announcements or malicious use" of CVE-2026-20133. CISA's listing, by contrast, cited "evidence of active exploitation" as the basis for cataloging the flaw. This divergence between a vendor's own disclosure posture and a government agency's characterization is increasingly common: CISA's catalog is based on intelligence and incident reporting that vendors may not have visibility into.
Catalyst SD-WAN Manager (formerly marketed as vManage) is a network management platform that allows administrators to monitor and control up to 6,000 Catalyst SD-WAN devices from a single dashboard. That centralized management function is precisely what makes vulnerabilities in it strategically attractive: compromise of the management plane gives an attacker visibility into, and potential control over, an organization's entire wide-area network fabric. CVE-2026-20133 is an information-disclosure flaw rather than a remote code execution bug, but sensitive configuration and credential material extracted through it could facilitate follow-on access.
CISA's order referenced its earlier Emergency Directive 26-03 and accompanying Hunt and Hardening Guidance for Cisco SD-WAN Devices, suggesting the agency has been tracking a broader pattern of Cisco SD-WAN exploitation rather than treating CVE-2026-20133 in isolation. Two related Cisco SD-WAN flaws, CVE-2026-20128 and CVE-2026-20122, were flagged as actively exploited in the wild one week after their initial February patches. In early March, Cisco additionally patched two maximum-severity vulnerabilities in its Secure Firewall Management Center software that could allow root access to the underlying operating system.

Citizens Bank and the Vendor Data Problem
On the same day, Citizens Financial Group confirmed it was investigating a vendor data incident after ransomware actors claimed to possess millions of customer records. The bank said operations were unaffected and that customer impact appeared limited, a statement consistent with the vendor-side breach pattern rather than a direct compromise of Citizens' own systems. The distinction matters: vendor breaches, in which a third-party service provider that holds customer data on behalf of a bank is compromised, have become one of the primary vectors for financial-sector data exposure precisely because they are outside the direct control of the institution whose customers are at risk.
The Citizens incident did not involve a confirmed CVE disclosure or a named ransomware family as of April 22. But it fits a pattern documented in the Cognyte LUMINAR 2026 Annual Threat Report: stolen credentials remain the entry point in 22 percent of data breaches, and dark web markets for such credentials remain liquid even as the volume of advertised credential listings fell roughly 50 percent in 2025 (to approximately 7 million listings). That volume decline reflects market consolidation around a small number of high-volume information-stealing tools rather than a reduction in actual credential theft activity. The Lumma infostealer alone was responsible for 2.2 million listings, representing roughly 42 percent of the total dark web credential market.
"We're seeing a fundamental shift in how cyber threats are carried out and scaled. AI, ransomware groups and nation-state actors are no longer separate challenges. They're increasingly working in tandem, creating attacks that move faster and are harder to detect."
Gilad Zahavi, VP of Threat Intelligence, Cognyte Software
The Cognyte report, released on the same day as the Citizens disclosure, adds important context. Its analysis of more than 2,300 real cyber incidents in 2025 found that AI enabled attackers to automate 80 to 90 percent of a specific nation-state espionage campaign, and that AI-generated content now accounts for 82.6 percent of phishing material. At the same time, the report documents the first known AI-orchestrated cyber espionage campaign using a large language model, a development Cognyte's analysts describe as qualitatively different from prior AI-assisted attacks.
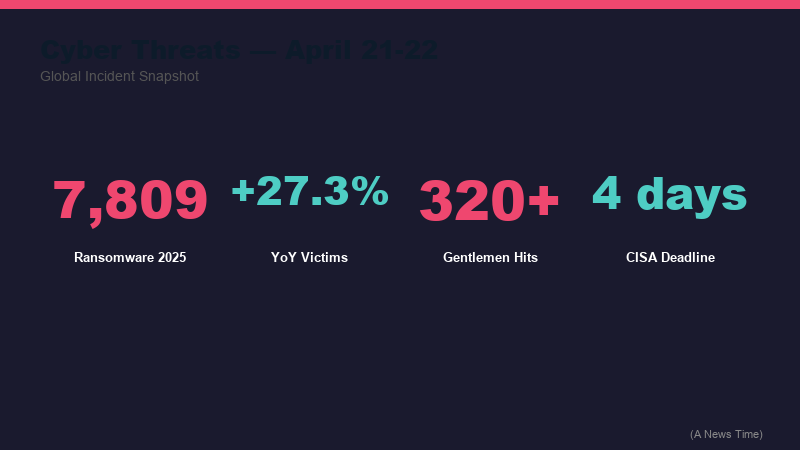
The Broader Pattern: What 7,809 Ransomware Victims Tells You
Pulling back to the full-year 2025 data in the Cognyte LUMINAR report, the threat landscape looks like this. Ransomware groups claimed 7,809 victims, a 27.3 percent increase from 2024. The United States accounted for roughly one-third of global ransomware incidents. Total ransomware payments actually fell 23 percent even as victim counts rose, which security analysts read as evidence that organizations are improving recovery capabilities while attackers have shifted their targeting toward small and medium-sized businesses that are less likely to have robust backup and incident response infrastructure.
| Incident | Category | Scope | Key Detail |
|---|---|---|---|
| Gentlemen RaaS | Ransomware | Enterprise-wide (320+ victims) | Cross-platform: Windows, Linux, ESXi; Go + C lockers; 1,570-host botnet |
| Cisco CVE-2026-20133 | Actively exploited vulnerability | Federal agencies + enterprises | SD-WAN Manager info disclosure; CISA 4-day patch deadline |
| Citizens Bank vendor breach | Data exposure claim | Financial sector | Ransomware actors claim millions of records; bank says limited customer impact |
| Cognyte LUMINAR 2026 Report | Threat intelligence | Global | 7,809 ransomware victims in 2025; AI automating 80-90% of specific espionage campaigns |
The Qilin ransomware group led all operators with 12.8 percent of global victims. Nation-state activity accounted for 56.6 percent of incidents in the Middle East and 67 percent in the Asia-Pacific region, while cybercriminal groups led in North America at 52 percent. The Linux Kernel had the highest number of reported vulnerabilities in 2025, at 2,257, while nearly 50,000 new vulnerabilities were disclosed across all platforms at an average CVSS score of 6.6.
For related coverage, see our earlier reporting on OpenAI's GPT-5.4 cybersecurity deployment for defenders, on Anthropic's Project Glasswing cyberdefense AI initiative, and on the European Commission data breach via AWS cloud infrastructure. The thread running through all of these is consistent: the attack surface is widening faster than most organizations can respond.
What Organizations Should Do Now
The Gentlemen, Cisco, and Citizens incidents each suggest different but overlapping defensive priorities. Against Gentlemen-style enterprise ransomware, Check Point's own recommendations focus on hardening domain controllers, restricting Group Policy Object changes, monitoring for lateral movement tools like Cobalt Strike and AnyDesk, and enforcing strong network segmentation between hypervisor management interfaces and user environments. The Gentlemen group's ability to weaponize Group Policy for domain-wide payload deployment is particularly significant: it means that any attacker who reaches domain admin level can effectively treat every domain-joined system as a single target.
Against the Cisco SD-WAN exploitation pattern, the straightforward action is applying the vendor patches, but CISA's broader guidance in Emergency Directive 26-03 includes network-level hunting for signs of prior compromise, not just patch application. Given that CVE-2026-20127, the critical authentication bypass in Cisco SD-WAN, was being exploited as a zero-day since at least 2023 before Cisco publicly documented it, organizations should treat their SD-WAN management planes as potentially already compromised pending a forensic review rather than assuming patching closes a previously clean environment.
Against vendor-side data exposure, the Citizens incident illustrates why third-party risk management programs have become a board-level concern rather than a procurement checkbox. An organization's own security posture is increasingly only as strong as its weakest vendor's posture, and ransomware actors have learned to target the vendors that hold the most data on behalf of the most clients.
The Cognyte LUMINAR data on AI-assisted attacks deserves its own response. AI-generated phishing content at 82.6 percent of total phishing volume means that the traditional signal of poorly written, grammatically awkward phishing emails is no longer reliable as a detection heuristic. Employees who have been trained to spot "obvious" phishing language need updated training that focuses on context and request patterns rather than prose quality. The email asking you to reset your credentials might now read perfectly.
Frequently Asked Questions
What is the Gentlemen ransomware group?
Gentlemen is a ransomware-as-a-service operation that emerged around mid-2025. It operates cross-platform lockers written in Go (for Windows, Linux, NAS, and BSD) and a separate C-based locker for VMware ESXi hypervisors. Affiliates follow a disciplined intrusion playbook using tools like Cobalt Strike, Mimikatz, and AnyDesk, and the group uses a Tor-hosted leak site to publish stolen data when victims refuse to pay. Check Point Research reported more than 320 victims as of April 2026.
What is CVE-2026-20133 and why did CISA issue an emergency order?
CVE-2026-20133 is an information-disclosure vulnerability in Cisco Catalyst SD-WAN Manager that allows unauthenticated remote attackers to access sensitive data by querying the device's API. Cisco patched it in late February 2026. CISA added it to its Known Exploited Vulnerabilities catalog on April 21, 2026, citing evidence of active exploitation, and ordered Federal Civilian Executive Branch agencies to apply mitigations by April 24, 2026.
How many ransomware victims were there globally in 2025?
Cognyte's LUMINAR 2026 Annual Threat Report, released April 21, 2026, documented 7,809 ransomware victims claimed by ransomware groups worldwide in 2025, a 27.3 percent increase year over year. The United States accounted for roughly one-third of global incidents. Despite the victim count increase, total ransomware payments fell 23 percent, suggesting organizations are improving their recovery capabilities.
How is AI being used in cyberattacks?
According to the Cognyte LUMINAR 2026 report, AI is being used to automate up to 80 to 90 percent of specific nation-state espionage campaign tasks, and AI-generated content now makes up 82.6 percent of phishing material. Cognyte also documented what it describes as the first known AI-orchestrated cyber espionage campaign using a large language model. On the defensive side, LLM-assisted tools have been used to identify zero-day vulnerabilities, including CVE-2025-6965.
What should enterprises do first in response to the Gentlemen ransomware threat?
Check Point Research recommends prioritizing hardening of domain controllers, restricting who can create or modify Group Policy Objects, monitoring for known lateral movement tools (Cobalt Strike, AnyDesk, SystemBC), enforcing network segmentation between hypervisor management interfaces and production environments, and implementing endpoint detection and response solutions that can catch the Defender-disabling commands Gentlemen affiliates use during the pre-encryption phase.
Sources
- DFIR Report: The Gentlemen Ransomware-as-a-Service Operation, Check Point Research
- CISA flags new SD-WAN flaw as actively exploited in attacks, BleepingComputer
- Cognyte 2026 Threat Landscape Report: AI Accelerates Cyber Threats as Ransomware Surges Worldwide, Business Wire
- CISA Known Exploited Vulnerabilities Catalog, CISA.gov












